Every news outlet and fool politician is banging on about the idea that Brexit has led to a shortage of 100,000 lorry drivers in the UK. This story is too good to check for those still smarting over the lost referendum, or have some other axe to grind. Unfortunately for them, I have checked the story, and it’s a pretty shabby state of affairs.
Let’s start with this figure of 100,000. It comes from the Road Haulage Association, a lobby group. And they claim to have calculated it.
When pushed, it all gets a bit vague, and it might surprise you to know that they were claiming a shortage of 50,000 in 2015 – before anyone had heard of Brexit. They always claim a shortage of about this number. They say it was calculated by surveying their members, and other means – such as looking at vacancies. They also subtract the number of drivers registered with them from the number of lorries registered with the DVLA and add that. Seriously.
Tesco has recently stated it needs another 800 drivers. A quick look at their staff vacancies adverts shows they’re actually looking for just three.
Richard Walker from Iceland, another arch-Europhile, has taken the opportunity to get his mug into newspapers by talking about “Cancelling Christmas”. This is the same Richard Walker who gets publicity for environmental initiatives yet flies around in a private helicopter.
The Road Haulage Association will also tell you there are about 600,000 lorry drivers in the UK. The Office for National Statistics, which knows what people do for a living, reckons there are half that number. Again, the RHA is counting the wrong thing – HGV licenses. Just because someone has an HGV license it doesn’t mean they’re actually a lorry driver. Many people, myself included, have one so I can hire a lorry when I need one – such as for transporting stuff to Scout camps. At the time I got it, the cost was £70. It’s not unreasonable to want to drive something large privately.
Another group with HGV licenses are firemen. Those big red things they drive around in are too big to be classified as cars, so they do the HGV test. I believe Princess Anne had one once, so she could drive large horse boxes.
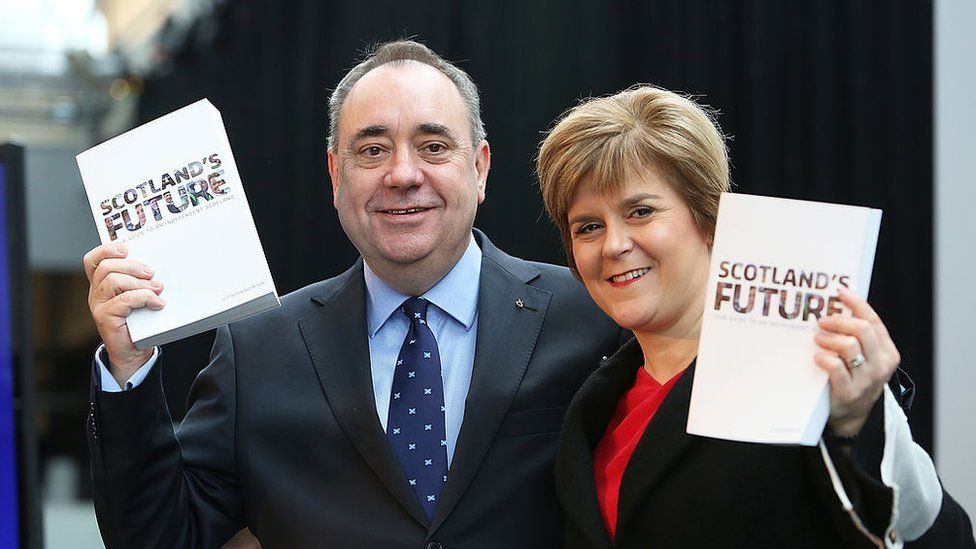
So I’m not going to take anything the Road Haulage Association takes seriously until they use better methods for obtaining their statistics. It’s almost as if they had an agenda. Actually… it’s a lobby group and its head – Richard Burnett – is a long-time campaigner against Brexit (and by extension the present government).
So what is the truth of the matter if you go to a sober source such as the ONS for figures? There is indeed a shortage of HGV drivers – they say the number has dropped by 55,000 in the last 18 months, of which 47,000 were the last year. However, this isn’t caused by Brexit. In Q2 2020 there were 25,000 EU drivers working in Britain; a year later there are 24,350. This is about the same as the 2015 figure. There was, however, a blip in numbers, peaking at 42,460 – and that happened after Brexit. This fell as drivers returned home during the pandemic; boring but true. And it’s only a minor factor in the current shortage. About 12,500 lost drivers out of 55,000 (18%) were EU nationals. Every country across Europe is reporting similar shortages, apart from Romania as far as I can tell. They’re also complaining in the USA; as far away from Brexit as you can get.
In reality, far the largest drop in working driver numbers comes from retirement – or more accurately leaving to find other jobs. It’s as simple and boring as that. But the story doesn’t end there, as it’s also been claimed that more people are retiring than passing tests. Unfortunately the figures don’t bear this out either.
In 2010-2014 there were 15,500 new licenses issued, with 7500 retiring. In the second half of the decade there were 25,500 new licenses and 8600 retiring. The fact is that there are 230,000 licensed drivers under the age of 45 alone in the UK who are choosing not to drive commercially. They’ve got fed up and taken other jobs, or are using the license privately. The average age of British lorry drivers is now about 55, clearly pointing to trouble ahead.
If you want to figure out what’s going on behind the headlines, and the Twitter experts who have never even driven a lorry in their lives, you eventually end up following the money. In this case the RHA (a lobby group, remember) is making the case for the government to favour their sector. Of course they’re going to highlight any problem, and demand the government does something about it – and more specifically, throw money at it. The thing is that the logistics industry hires their own strategic planners; experts in the field of logistics. They should have seen this coming and done something about it, instead of bleating for the government to bail them out now.
The truth may be simple; if the pay and conditions for lorry drivers were better, more people would do it. And that’s entirely up to the logistics companies to solve. Some have undoubtedly been using cheap foreign labour in the last few years, which has gone home during the pandemic – and they’re the ones that have been hit the worst. And now they want the taxpayers to bail them out for having treated their drivers badly.
Update
Now we’re being told that 5000 visas are being made available to hire in foreign drivers. That’s great. But why would foreign drivers from the EU even want to work here? There’s a shortage across Europe, and they have better conditions working there. France, Germany and Belgium have laws that mean drivers don’t have to work on Sundays. And if you’ve ever compared a French and British transport cafes, the continentals win hands-down.
Update 2
So now Richard Burnett (RHA) has started panic buying of fuel by claiming there was going to be a shortage due to the lack of tanker drivers, and the hysterical media has picked it up. I’m sure the timing has nothing to do with the Labour Party conference.
Sources:
All figures in this article come from the Office for National Statistics, the Road Haulage Association or European/American government sources. I’ll make the ONS spreadsheets (the reliable stuff) available when I can figure out how.